CraxsRatTakes full control of your phone.Is your device protected?
New Android threats are smarter than your antivirus. We show you what to look for and how to protect your phone properly.
New Android threats are smarter than your antivirus. We show you what to look for and how to protect your phone properly.
Answer 12 quick questions to find out if your Android device shows signs of CraxsRat infection.
This takes less than 90 seconds. No data is collected — everything runs in your browser.
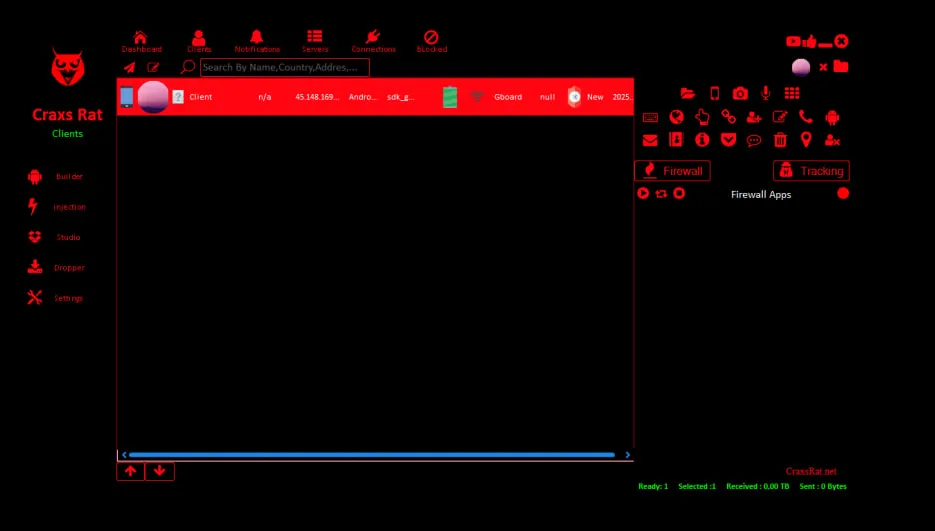
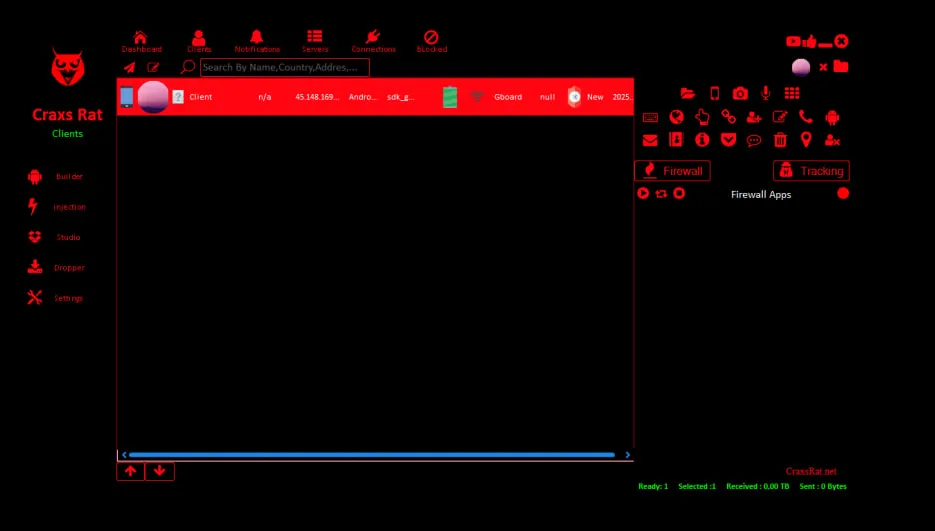
What CraxsRat is actually capable of.
Attackers treat your device as their own. They can view your screen live, swipe, type, and open apps remotely even while the phone is locked.
Malware can forcibly wake your screen and unlock it using captured PINs or patterns to perform actions when you aren't looking.
Logs every tap and keystroke. Attackers see everything you type: passwords, messages, search history, and 2FA codes.
Automatically detects and drains cryptocurrency wallets. It also intercepts SMS 2FA codes to bypass banking security.
Silently uploads your photos, videos, and documents to a C2 server. Attackers can delete or encrypt your files for ransom.
Activates front/back cameras and microphone without indicators. Attackers can watch and listen to your surroundings in real-time.
How a simple mistaken click turns into a total device takeover.
Users are tricked into downloading malicious APKs from fake websites, SMS phishing loops, or 'modded' app stores.
The malware requests 'Accessibility Service'. Once granted, it can automate clicks, grant itself Admin rights, and prevent uninstallation.
The device connects to a Command & Control (C2) server. Attackers now have full remote access to steal files, credentials, and track location.
Once the Accessibility Service is enabled, CraxsRat's automated script executes instantly. Your device is fully under attacker control before the settings close.
Real-world CraxsRat incidents documented by Group-IB, Cyfirma, Kaspersky, SOCRadar, and ESET. Click any marker to view campaign details and source citations.
A comprehensive breakdown of every documented CraxsRat campaign, including attack vectors, targeted sectors, technical indicators, and the malware's evolution from 2020 to 2025. All data sourced from published threat intelligence reports by leading cybersecurity firms.
Developer "EVLF" begins building CraxsRat from Syria. Early versions focus on basic remote access capabilities including SMS interception, call recording, and file browsing. The RAT is initially marketed alongside CypherRAT on underground forums.
CraxsRat lifetime licenses go on sale through Telegram channels and dark web marketplaces. Pricing ranges from $100 to $500 for lifetime access. The malware gains traction among Arabic-speaking threat actors due to its user-friendly builder interface and Arabic-language documentation.
Major feature updates add VNC (Virtual Network Computing) for real-time screen control, accessibility service abuse for overlay attacks, and cryptocurrency wallet targeting. Cracked versions begin appearing on Telegram, dramatically expanding the user base beyond paying customers. Over 100 legitimate licenses sold by this point.
CraxsRat deployment explodes globally. Group-IB documents major banking phishing campaigns in Singapore targeting 10+ brands. The "Dark Strom" hacker group begins selling CraxsRat v6.7 on Telegram. South Asian countries see massive adoption through WhatsApp distribution and APK sideloading. Eastern European data centers emerge as primary C2 (Command & Control) infrastructure hosting locations.
Group-IB discovers over 190 CraxsRat samples specifically targeting Malaysian banking, retail, infrastructure, food & beverage, delivery, and logistics sectors. Phishing websites mimicking legitimate Malaysian brands serve as primary distribution vectors. CraxsRat is increasingly bundled with regional banking trojans in Latin America. EVLF's total earnings exceed $75,000 from license sales alone.
Cyfirma documents G700, an advanced CraxsRat variant with enhanced evasion techniques including anti-emulator detection, encrypted C2 communications, and runtime code injection. G700 specifically targets cryptocurrency wallets (MetaMask, Trust Wallet, Coinbase) and financial applications. The variant demonstrates increased sophistication in bypassing Google Play Protect and third-party antivirus solutions.
CraxsRat was developed by a threat actor known as "EVLF" operating from Syria. Cyfirma's research identified the developer through cryptocurrency transaction analysis, Telegram activity patterns, and infrastructure registration records.
Group-IB documented a sophisticated phishing campaign targeting Singaporean users, operated by Chinese-speaking threat actors. Attackers impersonated well-known local brands to distribute CraxsRat-infected Android applications.
The largest documented CraxsRat campaign by sample volume. Group-IB discovered over 190 unique malware samples targeting six major Malaysian economic sectors through convincing phishing websites that mimicked legitimate local businesses.
SOCRadar documented the hacker group "Dark Strom" actively selling CraxsRat version 6.7 through Telegram channels. The marketplace model allowed low-skill attackers to launch sophisticated mobile malware campaigns with minimal technical knowledge.
South Asia (India and Pakistan) represents the highest-volume infection region for CraxsRat due to the prevalence of Android app sideloading and low Google Play Protect adoption rates. Malware spreads primarily through WhatsApp groups sharing modified APK files.
Lookout documented targeted CraxsRat campaigns across the UAE and Saudi Arabia leveraging sophisticated social engineering through WhatsApp. Attackers deployed malware through fake government service applications and fraudulent cryptocurrency investment platforms.
Multiple documented CraxsRat campaigns trace their Command & Control (C2) infrastructure to data centers in Eastern Europe. These servers handle all communication between infected devices and attacker control panels, including data exfiltration and remote command execution.
Group-IB identified the operators behind the Singapore banking campaigns as Chinese-speaking threat actors based in East Asia. These operators used CraxsRat alongside custom Android payloads for comprehensive credential harvesting operations targeting Southeast Asian financial institutions.
ESET Research documented a growing underground marketplace for CraxsRat across North African Telegram channels. The region serves as a secondary distribution hub for Arabic-speaking threat actors, with localized Telegram groups offering tutorials, cracked versions, and technical support for CraxsRat deployment.
Kaspersky's mobile threat report highlights Sub-Saharan Africa as an emerging CraxsRat infection region. Budget Android devices sold in the region often lack security updates and Google Play Protect coverage, making users particularly vulnerable to sideloaded malware including CraxsRat.
Recorded Future documented CraxsRat being bundled with regional banking trojans targeting Latin American financial institutions. Brazilian banking customers were primary targets, with distribution through fake banking apps and SMS phishing (smishing) campaigns directing victims to malicious download pages.
Cyfirma published a detailed technical analysis of G700, the next-generation evolution of CraxsRat. G700 features advanced anti-analysis capabilities, encrypted C2 communications, and specifically targets cryptocurrency wallets and financial applications. This variant represents a significant escalation in CraxsRat's technical sophistication.
Intelligence data compiled from published research by:
Group-IB • Cyfirma Research • Kaspersky Lab • SOCRadar • ESET Research • Lookout Threat Intelligence • Recorded Future
Last updated: March 2025. All campaign data reflects publicly documented incidents and threat intelligence assessments.
See why CraxsRat is much more dangerous than other spyware apps.
| Capability | CraxsRat | Other RATs | Legit Apps |
|---|---|---|---|
| Remote Access Control (VNC) | |||
| Live Screen Mirroring | Sometimes | ||
| Keylogging & Passwords | |||
| SMS & 2FA Extraction | |||
| Overlay & Phishing Injection | Rarely | ||
| Stealth Mode & Persistence | Sometimes | ||
| Play Protect Bypass | Not well | ||
| Live Mic & Camera Feed | Only with Permit |
Stay one step ahead. Follow these simple tips to stop spy apps before they get inside.
Only download apps from the Google Play Store. Never install from suspicious links, Telegram channels, or 'cracked' APK sites.
Immediately revoke permissions if a calculator or game asks for 'Accessibility' or 'Device Admin'. These are critical red flags.
Ensure 'Google Play Protect' is active in your settings. It scans your device daily for known malware signatures.
Install Android security patches immediately. They fix critical vulnerabilities (CVEs) that spyware exploits to gain access.
Hackers use urgency. Verify the sender before clicking links in SMS or DMs. Never download files from unknown chats.
Run periodic scans with established antivirus solutions (e.g., Avast, Bitdefender) to detect hidden threats.
Read our newest articles and learn how to stay safe with our expert guides.
Technical documentation of the CraxsRat Remote Access Trojan (RAT), detailing its command and control structure, permission abuse, and infection vectors.
A defensive framework for protecting Android endpoints from modern remote access threats, focusing on attack surface reduction and permission auditing.
In-depth technical analysis of the obfuscation, anti-emulator, and dynamic loading techniques used by the latest CraxsRat variant.
Quick answers to the most common questions about CraxsRat and Android security.
We'll email you when we find a new CraxsRat version, a new Android malware, or a new botnet.
🔒 By subscribing you agree to our Privacy Policy. Unsubscribe anytime.