CraxsRAT and BT Mob RAT: The Android Spyware Built by the Same Hacker
Comprehensive analysis of CraxsRAT and BT Mob RAT Android spyware families developed by EVLF, including infection methods, capabilities, real-world campaigns, and protection strategies.
Pretty Hax Intelligence Research
Security Research Team
Introduction
CraxsRAT and BT Mob RAT are popular Android malware families recognized for their powerful Remote Administration Tools (RAT). Both provide attackers with extensive remote device control and advanced spyware functions — including keylogging, gesture control, and the silent recording of cameras, screens, and calls.

Background: The Evolution of Android Spyware
CraxsRAT developed in 2020 as a modified version of the leaked Spymax RAT source code. Developed by a hacker and malware developer known as EVLF, many hackers and scammers started to search for him on underground forums, dark web, and Telegram channels. This way he gained his popularity.
By offering a GUI-based builder, EVLF helped cybercriminals to generate highly advanced and custom malicious payloads APK. CraxsRAT became popular for abuse of Android Accessibility Services to control full Android device.

Following the success of CraxsRAT, EVLF introduced BT Mob RAT (initially tracked by researchers alongside SpySolr) in late 2024. Building upon CraxsRAT's core code, he later built an advanced version called BT Mob RAT. It has upgraded techniques such as WebSocket-based Command and Control (C2) communication for real-time execution and credential theft via web injections.
Today, BT Mob RAT continues to be actively maintained, heavily marketed via Telegram channels and underground forums. Common people fall for this RAT and lose their money and data.
What Is CraxsRAT?
CraxsRAT is an Android remote access trojan. This is an advanced user-friendly Android RAT that can control your full device remotely. Once you install this RAT APK file on your device, the hacker or scammer can control your full device remotely.
According to Group-IB's analysis, CraxsRAT started as a modified version of an older RAT called SPYMAX RAT. Spymax was originally developed in 2019, but its source code was leaked on underground hacking forums in 2020.
Instead of just copying the leaked source code, EVLF used it as a blueprint. He modified the source code, improved its functionality, added new features, and integrated advanced capabilities like Google Play Protect bypass and obfuscation.
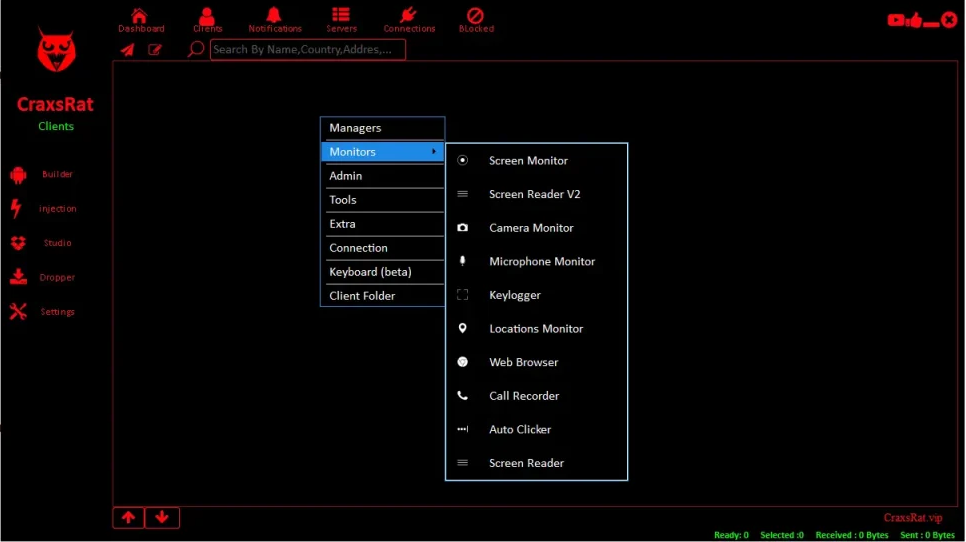
Key Features of CraxsRAT
- Keylogger — Record your keystrokes, including passwords and messages
- Live screen viewing — Attacker can watch and control your screen in real time
- Silent camera and mic access — They can spy on you and listen to your surroundings without any notification
- SMS interception — Steals one-time passwords (OTPs) from your bank, email, or social media
- File access — Downloads your photos, videos, documents, and anything else stored on your device
- GPS tracking — It can track your live location
- Auto unlock — It can unlock your device remotely
- Anti uninstall — It can prevent uninstallation from your device
The "Build Your Own Malware" Problem
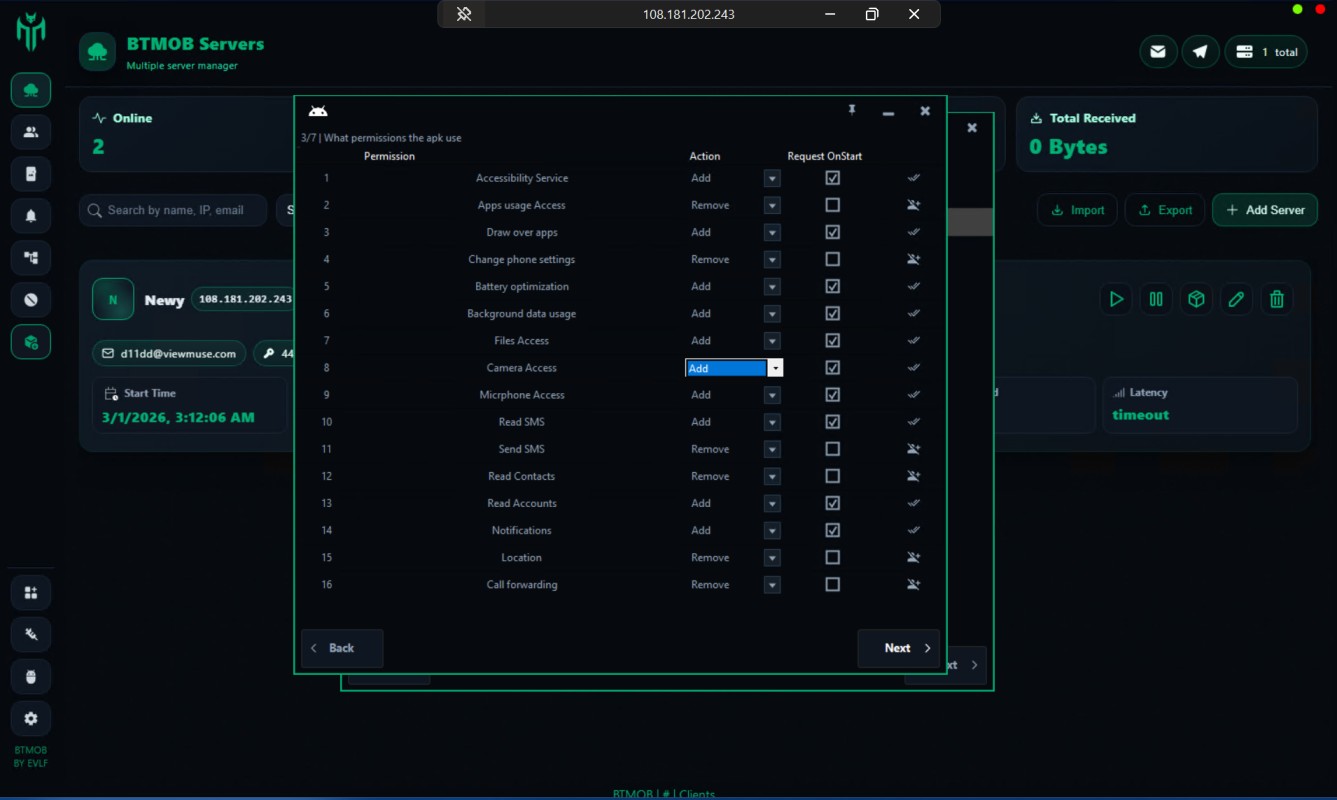
CraxsRAT comes with a GUI based builder. Think of it like a drag-and-drop app creator — except the app it creates is spyware. A buyer with zero coding skills can generate a working advanced malicious APK in minutes.
According to The Hacker News, it can crash the Settings page when a victim tries to uninstall the malicious APK from the device. Because it uses accessibility services to do so, it can simulate taps on your screen to grant itself admin rights and other permissions, disable security notifications, and prevent you from uninstalling it — often in less than a second.
What Is BT Mob RAT?
BT Mob RAT is the newer project from the same developer. Cyble Research and Intelligence Labs (CRIL) identified it as an evolution of yet another tool called SpySolr — and confirmed that the developer behind it is EVLF.
This is the same person who built CraxsRAT, took a short "break," and then came back with a new and improved version under a different name.
What BT Mob RAT Can Do
- Live screen sharing — Uses skeleton mode so that it can silently control the screen without user notice (no green dot)
- Better dropler — Can bypass Android 16 accessibility restrictions
- Credential theft — Through web injections and keylogging
- Remote device unlocking — Captures screen lock PIN and pattern to unlock it remotely
- SMS and Call Forwarding — Forwards all SMS and calls to the attacker
- Crypto mining — Mines Monero (XMR) cryptocurrency on the victim's device
- WebSocket-based communication — With command-and-control (C2) servers for real-time command execution
Who Is EVLF? The Developer Behind Both RATs
EVLF is not some mysterious person on the dark web. Cybersecurity firm Cyfirma actually unmasked the person behind the alias in August 2023.
Their investigation revealed a threat actor operating out of Syria, active for over eight years in the cybercrime scene.
How Cyfirma Caught EVLF
Cyfirma tracked EVLF's cryptocurrency transactions and discovered a wallet with over $75,000 earned from selling RATs over a three-year period. They contacted the crypto wallet provider and successfully got the funds frozen.
Here is the interesting part — EVLF tried to resolve the freeze by posting on a cryptocurrency discussion forum. That post gave Cyfirma additional information: a real name, usernames, an IP address, and an email address.
As SecurityWeek reported, EVLF ran a Telegram channel with over 10,000 subscribers and had sold lifetime licenses for CraxsRAT and CypherRAT to more than 100 threat actors.

Come Back After a Short Break
In August 2023, EVLF posted a message on their Telegram channel claiming they would "stop development due to Singapore govt pressure." Development did stop for a while, but EVLF came back with a new and improved version under a different name: BT Mob RAT.
The original channel was sold on September 5, 2023. But EVLF created a new channel and released CraxsRAT v7.5 on April 17, 2024. And then BT Mob RAT showed up later that year.
How CraxsRAT and BT Mob RAT Spread
These RATs don't "hack" into your phone using complex zero-day exploits. Instead, they rely entirely on social engineering. Their strategy is simple but highly effective: they trick you into downloading the malware yourself.
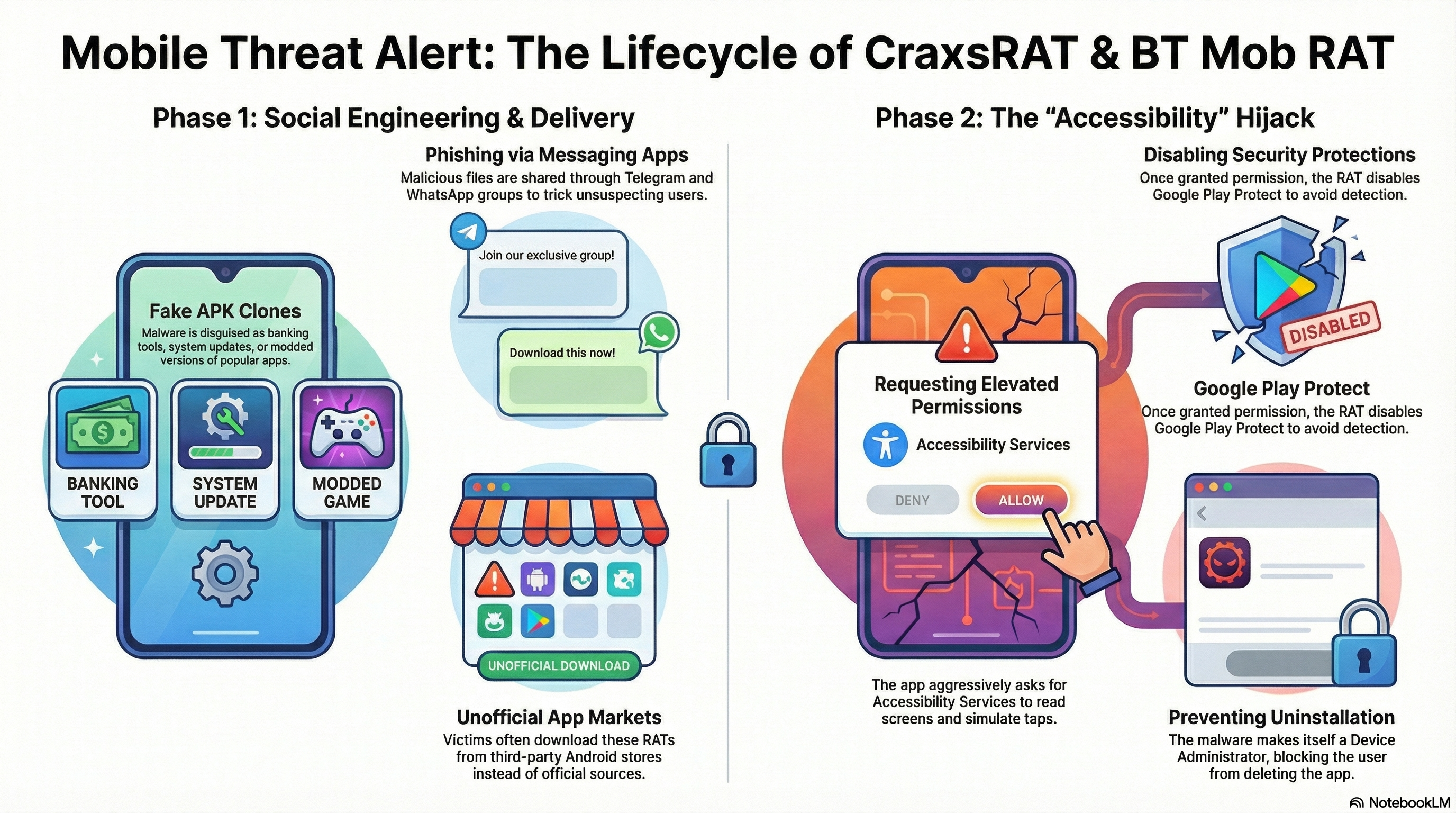
Common Infection Methods
- Fake APK files — The most common way to get infected is by downloading a clone APK file. Victims receive APK files disguised as system updates, popular apps, or banking tools.
- Phishing via messaging apps — Group-IB documented campaigns where attackers used Telegram and WhatsApp groups to share malicious APKs, often shown as modded apps.
- Fake app stores — CraxsRAT APK files often showing as popular apps have been found on unofficial Android markets.
- Targeted phishing — In campaigns aimed at businesses, malicious APK files have been delivered through phishing emails with APK attachments.
The Accessibility Services Abuse
Once installed, the malicious app aggressively asks for Android Accessibility Services permission. Most people tap Allow, thinking it's just a normal permission.
Accessibility Services was designed for disabled people to use their phones easily. But when a malicious app gets this permission, it can:
- Read everything on screen
- Simulate taps and swipes
- Grant itself additional permissions silently
- Make itself a Device Administrator, which prevents uninstallation
- Disable Google Play Protect
Real-World Damage: Operation DISTANTHILL
This is not a theoretical threat. CraxsRAT has been used in documented, large-scale campaigns that have caused real financial damage.

The Southeast Asia Campaign
In June 2024, a joint operation by the Singapore Police Force (SPF), Hong Kong Police Force (HKPF), and Royal Malaysia Police (RMP), dismantled a cyber fraud. The operation was codenamed "Operation DISTANTHILL."
Here are the numbers, as reported by Group-IB:
- More than 4,000 victims across Southeast Asia
- Singapore alone reported nearly 2,000 cases in 2023
- Total losses exceeded USD $25 million
- Over 250 phishing websites were used to distribute fake apps
- At least 260 variants of the RAT were found on command-and-control servers
- 16 arrests across Singapore, Malaysia, Hong Kong, and Taiwan
How to Know If Your Android Phone Is Infected
You do not need cybersecurity knowledge to spot the warning signs. Read below red flags:
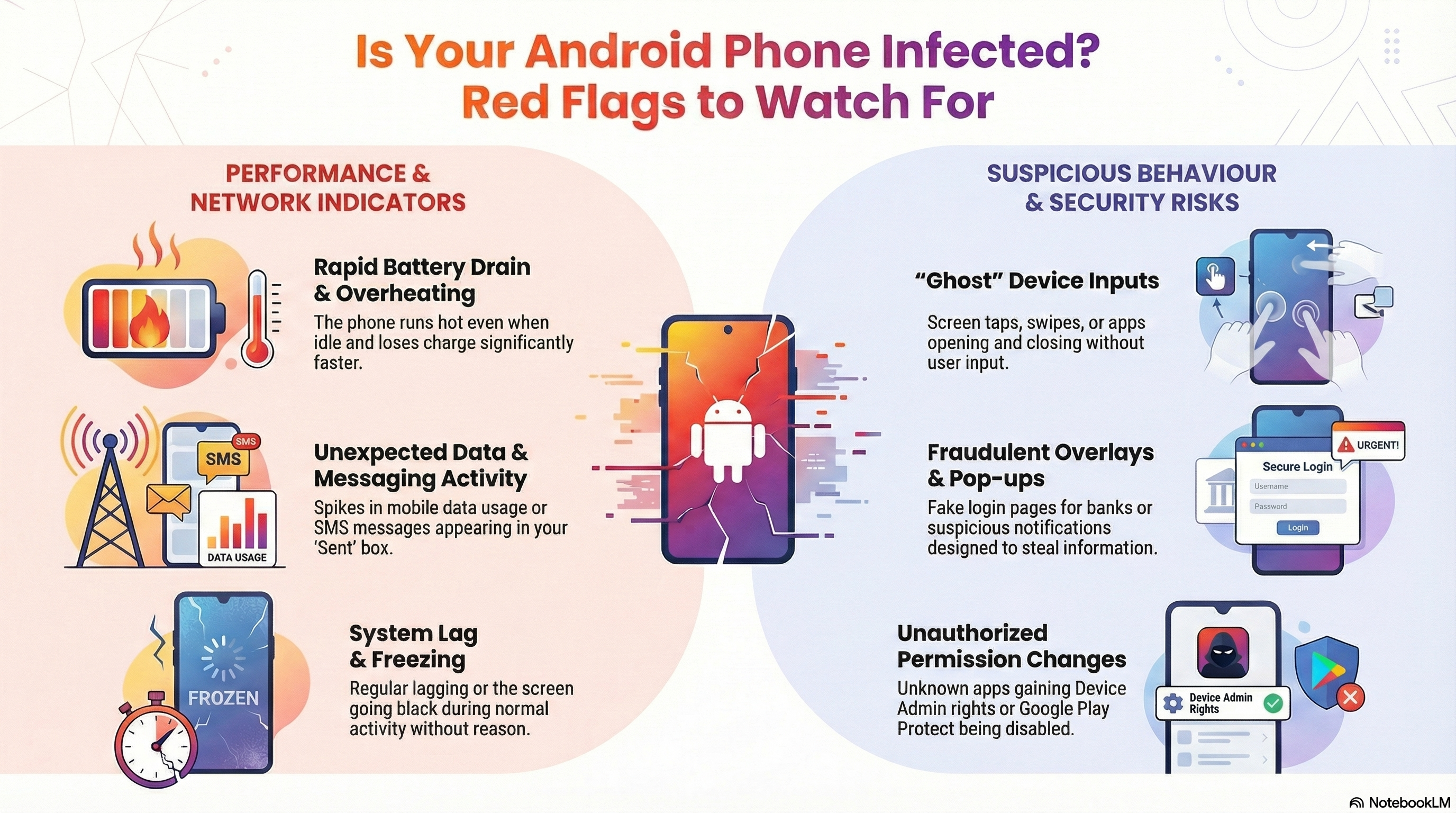
Performance Issues
- Phone runs hot even when idle
- Battery drains significantly faster than normal
- Regular freezing, lagging
Suspicious Network Activity
- Unexpected spikes in mobile data usage
- Outbound connections to unusual ports
- SMS messages in your "Sent" box that you did not send
Strange Device Behavior
- Screen taps, swipes or scrolls on its own
- Apps open or close without your input
- Screen goes black during normal activity without any reason
- Showing fake popups and notifications to steal your information
- Showing fake login pages of banks and other apps
Unusual Permission
- An unknown app has Device Admin rights (Settings > Security > Device Admin Apps)
- An unknown service is enabled under Accessibility settings
- Google Play Protect has been turned off without your knowledge
How to Protect Your Android Device
- Only install apps from the Google Play Store. This single rule prevents most common users from RAT APK installation.
- Never grant Accessibility permissions to random apps. If a shopping app, a game, or simple utility app asks for Accessibility Services, be careful.
- Check your permissions regularly. Go to Settings > Privacy > Permission Manager and check all apps permission regularly.
- Keep your phone updated. Android security patches fix the holes that RAT and other malware exploits.
- Do not trust links from strangers. A message on Telegram, WhatsApp or any other social media platform with a link or APK file — be careful.
How to Remove CraxsRAT if You Are Infected

- Disconnect immediately. Turn off Wi-Fi and mobile data. Switch on Airplane Mode.
- Boot into Safe Mode. Long-press the Power Off option until "Reboot to Safe Mode" appears.
- Uninstall the malware. Go to Settings > Apps, find the suspicious app, and uninstall it.
- Scan your device. Reboot normally. Install a reputable antivirus app and run a full scan.
- Secure your accounts. Using a different, clean device, change passwords for your email, banking apps, cryptocurrency wallets, and social media accounts.
If the RAT APK prevents you from uninstalling, do a factory reset of your device. Back up your photos and contacts to offline storage.
Frequently Asked Questions
FAQ: What is CraxsRAT?
CraxsRAT is an Android remote access trojan that gives attackers total control over a device. It can log keystrokes, view and control the screen live, access the camera and microphone, intercept SMS messages, steal files, and track GPS location.
What is BT Mob RAT and how is it connected to CraxsRAT?
BT Mob RAT is a newer Android RAT also developed by EVLF. It is based on an earlier RAT called SpySolr and shares core functionalities with CraxsRAT, including Accessibility Service abuse, credential theft, and remote device control.
How does CraxsRAT get on my phone?
Through clone or modded APK files spreading via phishing websites, Telegram and WhatsApp groups, and targeted phishing emails. It shows itself as legitimate apps — system updates, modded apps, or cracked apps.
Can Google Play Protect stop CraxsRAT?
Play Protect can detect known CraxsRAT signatures, but the malware uses heavy obfuscation and is distributed outside the Play Store. The most effective defense is not installing APKs from unknown sources.
Who is EVLF?
EVLF is a hacker and malware developer, living in Syria who created CraxsRAT, CypherRAT, and BT Mob RAT. Cyfirma unmasked their identity in August 2023 after tracking cryptocurrency transactions and freezing over $75,000 in a crypto wallet linked to malware sales.
Is CraxsRAT still active?
Yes. CraxsRAT v7.5 was released in April 2024. BT Mob RAT, built by the same developer, was identified in active campaigns in early 2025.
Has anyone been arrested for using CraxsRAT?
Yes. Operation DISTANTHILL in June 2024 led to 16 arrests across Singapore, Malaysia, Hong Kong, and Taiwan. The syndicate had defrauded over 4,000 victims with losses exceeding $25 million.
Sources and References
- Cyfirma — CraxsRAT Developer Unmasking Report
- Group-IB — CraxsRAT Technical Analysis
- Cyble — BT Mob RAT Analysis
- The Hacker News — EVLF DEV Unmasked
- SecurityWeek — CraxsRAT and CypherRAT Creator Exposed
Share This Article
📚 Related Articles
Technical Analysis: How CraxsRat V7.4 Evades Google Play Protect
In-depth technical analysis of the obfuscation, anti-emulator, and dynamic loading techniques used by the latest CraxsRat variant.
Malware ProfileCraxsRat Architecture: Technical Analysis of Android Spyware
Technical documentation of the CraxsRat Remote Access Trojan (RAT), detailing its command and control structure, permission abuse, and infection vectors.
Defense StrategyHardening Android Devices Against RATs: A Comprehensive Defense Guide
A defensive framework for protecting Android endpoints from modern remote access threats, focusing on attack surface reduction and permission auditing.